DCOMrade — Automating the enumeration of DCOM applications

During my internship at HackDefense I researched lateral movement techniques using the Distributed Component Object Model (DCOM), the built-in system to call software over the network from one Windows system to another. Part of this project was creating a script to enumerate DCOM objects that can be abused for lateral movement. My research is mostly based on Matt Nelson’s (a.k.a enigma0x3) earlier research. The script has also been converted to work with the Powershell Empire framework, at the time of writing this post the pull request is pending approval.
Introduction
My name is Axel Boesenach and I am currently an intern at HackDefense. Besides being an intern at HackDefense I also work part-time at Fox-IT as a SOC analyst and spend the rest of my free time researching / learning new stuff to challenge myself on a daily basis.
Background
The first time I saw DCOM being used as a means of moving laterally within Microsoft Windows domains / networks was while attending a workshop at Fox-IT, given by Eva Tanaskoska. I was immediately fascinated by the technique since it solely drives on built-in functionalities provided by the Microsoft operating system (living off the land). Seeing how it worked and why made me wonder: “Could this be automated in some way as to map out all the vulnerable points that can be activated using DCOM?”.
Research
As I’m approaching the finishing line with my studies I had to do an internship, and chose to research if it would be possible to automate the enumeration of potentially vulnerable DCOM applications. With the very helpful articles posted by Matt Nelson I managed to find a way to automate this enumeration process, something that would take a lot longer if done by hand.
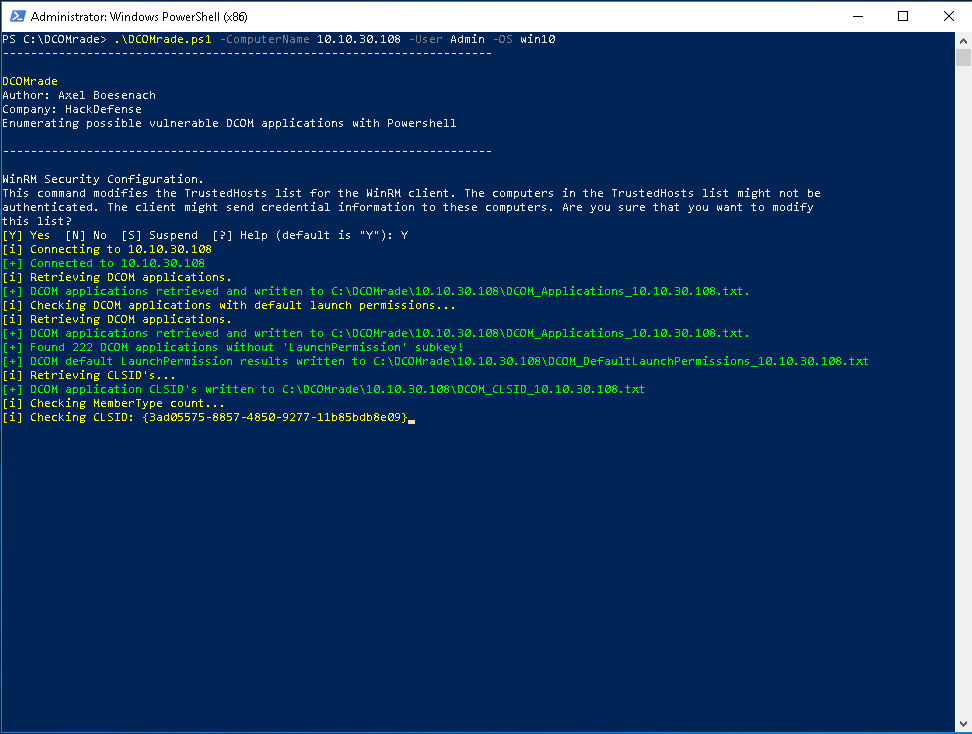
DCOMrade
The script that was created is a Powershell script that I called ‘DCOMrade’, a combination (and wordplay) of ‘DCOM’ and ‘enumerate’ while also being a pun on ‘comrade’. The script can be found on my Github accompanied by a research paper, that goes into the technical aspects of the idea, the solution and pieces of the script. The script has also been converted to work with the Powershell Empire framework which is waiting on approval at the time of writing this post.